Elite hackers associated with Russia’s military intelligence service have been linked to large-volume phishing campaigns aimed at hundreds of users in Ukraine to extract intelligence and influence public discourse related to the war.
Google’s Threat Analysis Group (TAG), which is monitoring the activities of the actor under the name FROZENLAKE, said the attacks continue the “group’s 2022 focus on targeting webmail users in Eastern Europe.”
The state-sponsored cyber actor, also tracked as APT28, Fancy Bear, Forest Blizzard, Iron Twilight, Sednit, and Sofacy, is both highly prolific and proficient. It has been active since at least 2009, targeting media, governments, and military entities for espionage.
The latest intrusion set, starting in early February 2023, involved the use of reflected cross-site scripting (XSS) attacks on various Ukrainian government websites to redirect users to phishing domains and capture their credentials.
The disclosure comes as U.K. and U.S. intelligence and law enforcement agencies released a joint advisory warning of APT28’s attacks exploiting an old, known vulnerability in Cisco routers to deploy malware known as Jaguar Tooth.
FROZENLAKE is far from the only actor focused on Ukraine since Russia’s military invasion of the country over a year ago. Another notable adversarial collective is FROZENBARENTS – aka Sandworm, Seashell Blizzard (née Iridium), or Voodoo Bear – which has engaged in a sustained effort to target organizations affiliated to the Caspian Pipeline Consortium (CPC) and other energy sector entities in Eastern Europe.
Both groups have been attributed to the General Staff Main Intelligence Directorate (GRU), with APT28 tied to the 85th Special Service Center (GTsSS) military intelligence unit 26165. Sandworm, on the other hand, is believed to be part of GRU’s Unit 74455.
The credential harvesting campaign targeted CPC employees with phishing links delivered via SMS. The attacks against the energy vertical distributed links to fake Windows update packages that ultimately executed an information stealer known as Rhadamanthys to exfiltrate passwords and browser cookies.
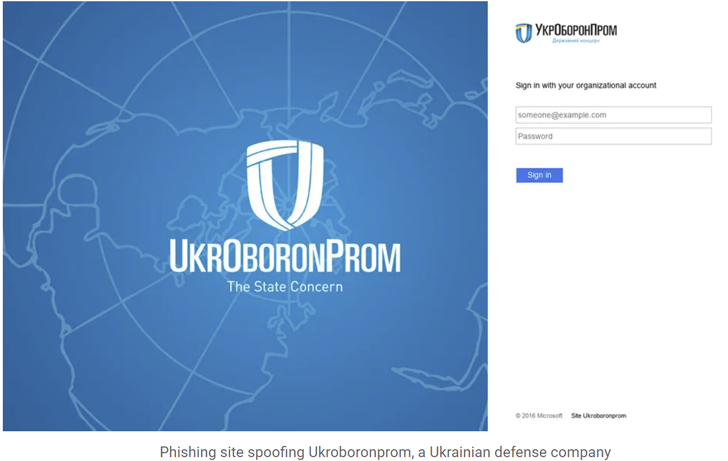
FROZENBARENTS, dubbed the “most versatile GRU cyber actor,” has also been observed launching credential phishing attacks targeting the Ukrainian defense industry, military, and Ukr.net webmail users beginning in early December 2022.
The threat actor is said to have further created online personas across YouTube, Telegram, and Instagram to disseminate pro-Russian narratives, leak data stolen from compromised organizations, and post targets for distributed denial-of-service (DDoS) attacks.
Zero Trust + Deception: Learn How to Outsmart Attackers!
Discover how Deception can detect advanced threats, stop lateral movement, and enhance your Zero Trust strategy. Join our insightful webinar!
“FROZENBARENTS has targeted users associated with popular channels on Telegram,” TAG researcher Billy Leonard said. “Phishing campaigns delivered via email and SMS spoofed Telegram to steal credentials, sometimes targeting users following pro-Russia channels.”
A third threat actor of interest is PUSHCHA (aka Ghostwriter or UNC1151), a Belarusian government-backed group that’s known to act on behalf of Russian interests and which carried out targeted phishing attacks singling out Ukrainian webmail providers such as i.ua and meta.ua to siphon credentials.
Lastly, Google TAG also highlighted a set of attacks mounted by the group behind Cuba ransomware to deploy RomCom RAT in the Ukrainian government and military networks.
“This represents a large shift from this actor’s traditional ransomware operations, behaving more similarly to an actor conducting operations for intelligence collection,” Leonard pointed out.
In all, the tech giant’s cybersecurity team, which works to counter nation-state hacking and attacks, said that Ukraine was at the receiving end of more than 60% of the phishing campaigns originating from Russia during the first three months of 2023.
The development also follows a new alert from the U.K. National Cyber Security Centre (NCSC) about emerging threats to critical national infrastructure organizations from state-aligned groups, particularly those that are “sympathetic” to Russia’s invasion of Ukraine.
“These groups are not motivated by financial gain, nor subject to control by the state, and so their actions can be less predictable and their targeting broader than traditional cyber crime actors,” the agency said.
