The Iranian threat actor known as MuddyWater is continuing its time-tested tradition of relying on legitimate remote administration tools to commandeer targeted systems.
While the nation-state group has previously employed ScreenConnect, RemoteUtilities, and Syncro, a new analysis from Group-IB has revealed the adversary’s use of the SimpleHelp remote support software in June 2022.
MuddyWater, active since at least 2017, is assessed to be a subordinate element within Iran’s Ministry of Intelligence and Security (MOIS). Some of the top targets include Turkey, Pakistan, the U.A.E., Iraq, Israel, Saudi Arabia, Jordan, the U.S., Azerbaijan, and Afghanistan.
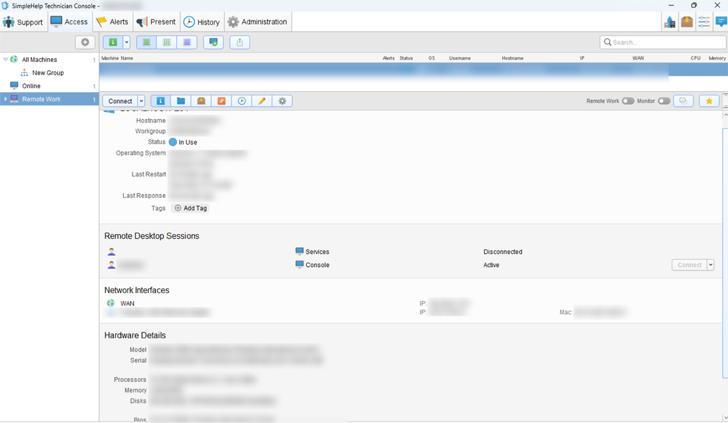
“MuddyWater uses SimpleHelp, a legitimate remote device control and management tool, to ensure persistence on victim devices,” Nikita Rostovtsev, senior threat analyst at Group-IB, said.
“SimpleHelp is not compromised and is used as intended. The threat actors found a way to download the tool from the official website and use it in their attacks.”
The exact distribution method used to drop the SimpleHelp samples is currently unclear, although the group is known to send spear-phishing messages bearing malicious links from already compromised corporate mailboxes.
Group-IB’s findings were corroborated by Slovak cybersecurity firm ESET earlier this January, detailing MuddyWater’s attacks in Egypt and Saudi Arabia that entailed the use of SimpleHelp to deploy its Ligolo reverse tunneling tool and a credential harvester dubbed MKL64.
Zero Trust + Deception: Learn How to Outsmart Attackers!
Discover how Deception can detect advanced threats, stop lateral movement, and enhance your Zero Trust strategy. Join our insightful webinar!
The Singapore-headquartered company further said it was able to identify hitherto unknown infrastructure operated by the group as well as a PowerShell script that’s capable of receiving commands from a remote server, the results of which are sent back to the server.
The disclosure comes weeks after Microsoft detailed the group’s modus operandi of carrying out destructive attacks on hybrid environments under the guise of a ransomware operation.
